How to create private endpoints in Azure?
This tutorial is based on Cantrill's Architecture on AWS Advanced VPC Section. The code is based on CloudFormation. We are going to implement this on Azure instead of AWS and use Terraform as our IaC.
This demo project is divided into three parts that will demonstrate our ability to configure secure VPC/VNET, especially in highly-regulated environments where data should be contained and highly compliant.
**🐋 DEMO PROJECT
0. [The Code**](https://github.com/asher-lab/asherl/tree/main/terraform/azure/Sample3-PrivateEndPoint)
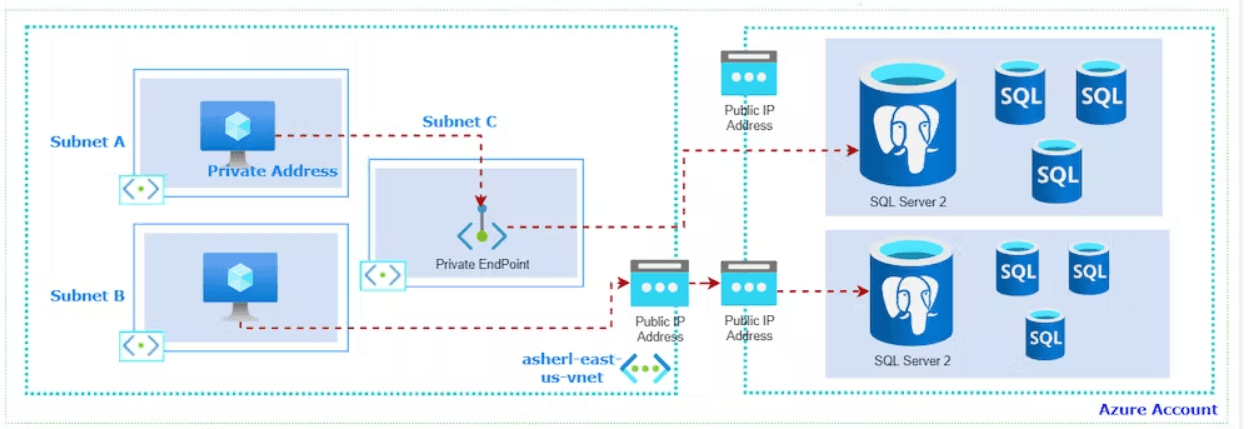
A. Architecture / End State
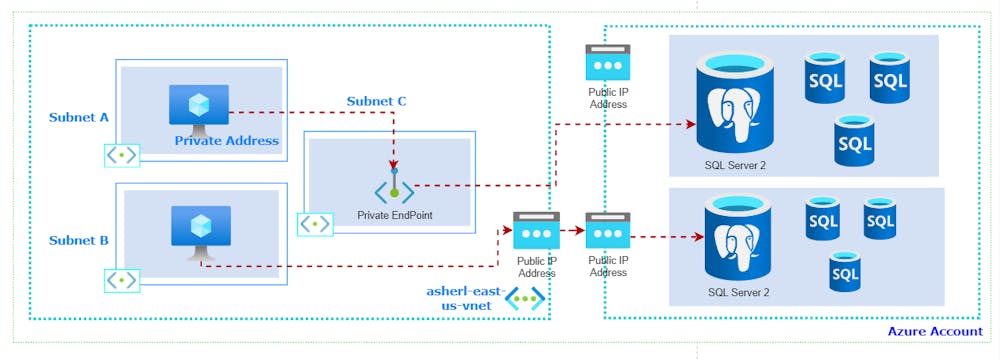
I created this Demo Architecture to help us get started with Azure Private EndPoints:
Check out (draw.io) it will help you create architectures easily.
B. Characteristics
- It has 3 subnets (Subnet A: Private Subnet. Subnet B: Public Subnet, Subnet C: For Private EndPoint).
- There are 2 Virtual Machines and 2 ways to access separate PostGres Database Servers. (One using a Private EndPoint and Other is using Public IP Address)
- This Cloud Architecture (CA) will demonstrate how you can implement PrivateEndPoint and to use PublicIP Address in accessing resources in Azure.).**
C. Steps
**1. Copy the Terraform Code
2. Disable Network Policies to create endpoint on your subnet
Copy
az network vnet subnet update --name subnet3 --resource-group ASHERL-US-DEV-rg --vnet-name ASHERL-US-DEV-vnet --disable-private-endpoint-network-policies true
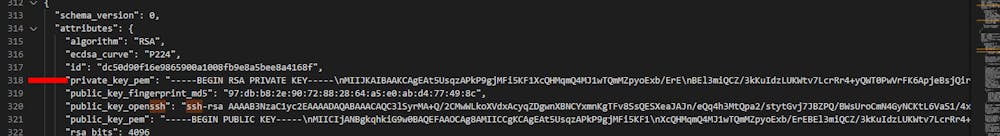
Extract the VM private key (.pem file) both on Public and Private Virtual Machine.
Currently this method is insecure, since it is located in the tfstate file. Take note this is for demo purposes only.Connect to two virtual machines, both public and private. (Be sure port 22 is open when you are trying to ssh).
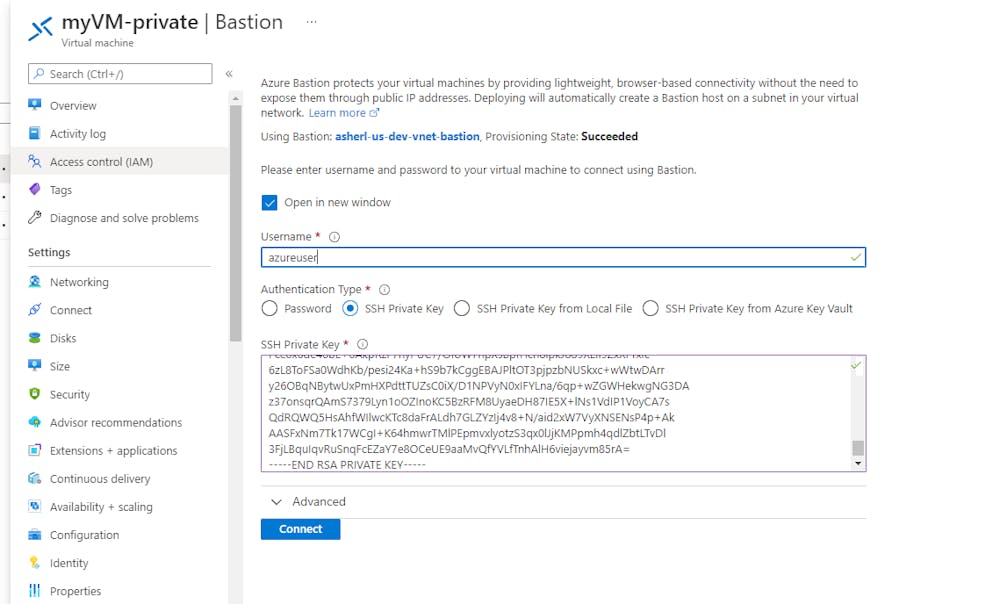
Connect to private instance via bastion:
As you can see, we are getting internet traffic on our public instance.

As per the private instance, we have traffic timeout.
D. Connect via Private EndPoint
Go to Azure Private EndPoint, then refer to documentation here:https://docs.microsoft.com/en-us/azure/search/service-create-private-endpoint https://techcommunity.microsoft.com/t5/azure-database-for-mysql-blog/using-terraform-to-create-private-endpoint-for-azure-database/ba-p/1279910
🧡 What's in here for AWS Users?
- AWS VPC Gateway Endpoint
- AWS Egress-Only Internet Gateway
- AWS (Network) Interface Endpoint
- AWS VPC Peering
- As I am looking for similar alternatives to AWS VPC Gateway Endpoint for Azure, the nearest implementation from the four services mentioned above are:
💙 What's in here for Azure Users?
- Azure Private EndPoints
- Azure Virtual Network Service EndPoint
- Azure Virtual Network Peering
🧡 AWS Discussion 🧡
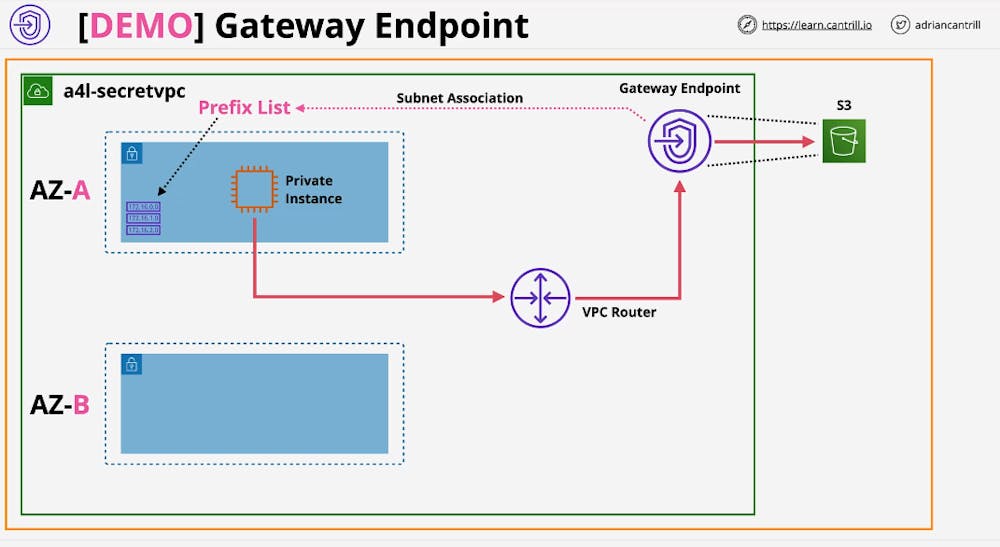
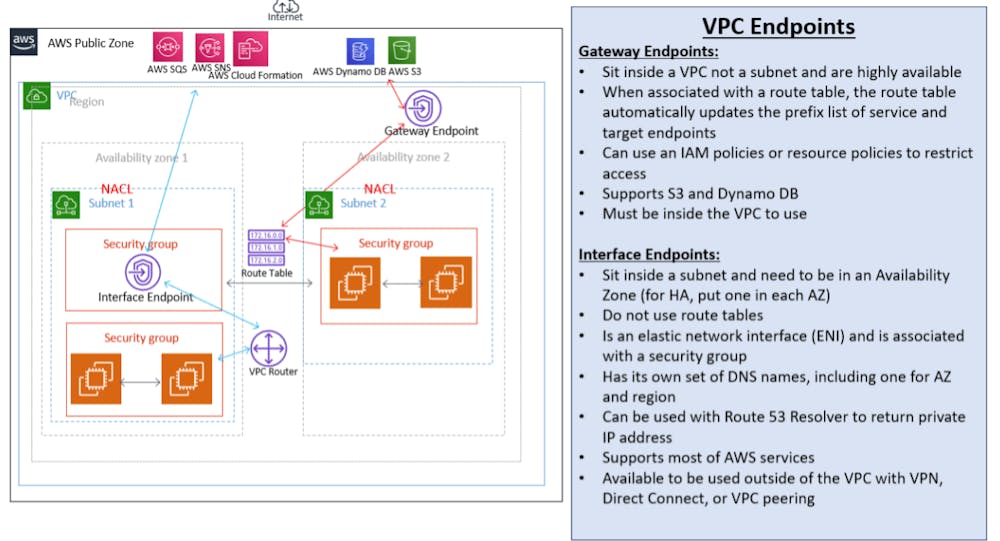
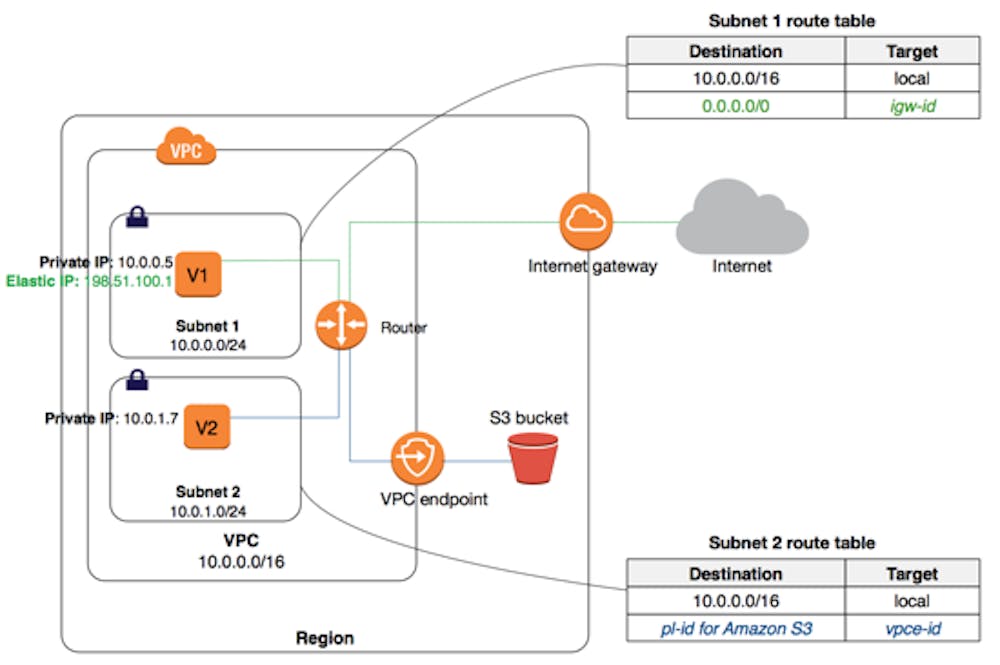
AWS VPC Gateway EndPoint
This architecture is useful incase you decided to make your AWS resources all in the private subnet. Meaning you don't want any trail or traffic of anything public in your architecture and you don't need to have a IGW, a VPN, or a public IP Address to access a specific Public endpoint such as S3 or DynamoDB in case of AWS. ( Or Some resources in storage account in case for Azure).
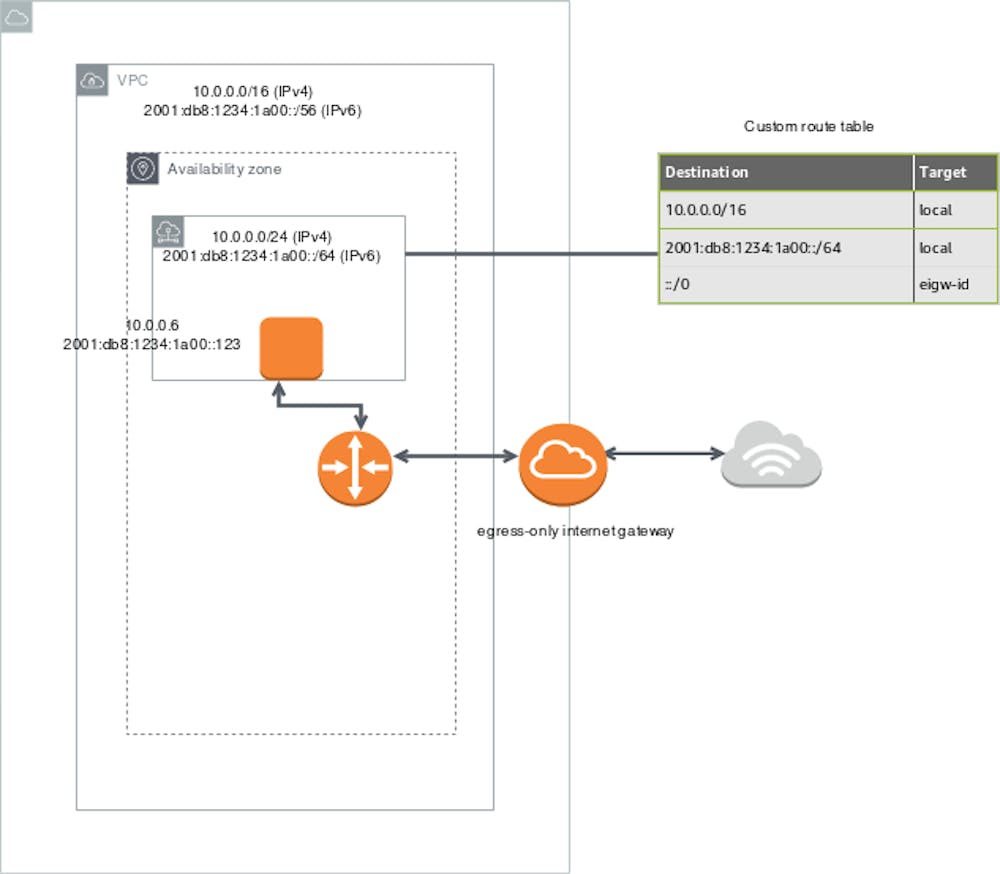
AWS Egress-Only Internet Gateway
In AWS, IPv6 does have limitation: you can't use NAT Gateway to block external traffic since it is not compatible. Via Egress-Only IG, you can customize your VPC in case you are using IPv6.
An egress-only internet gateway is a horizontally scaled, redundant, and highly available VPC component that allows outbound communication over IPv6 from instances in your VPC to the internet, and prevents the internet from initiating an IPv6 connection with your instances. (AWS).
To do this, create an egress-only internet gateway in your VPC, and then add a route to your route table that points all IPv6 traffic (::/0) or a specific range of IPv6 address to the egress-only internet gateway. IPv6 traffic in the subnet that's associated with the route table is routed to the egress-only internet gateway. (AWS).
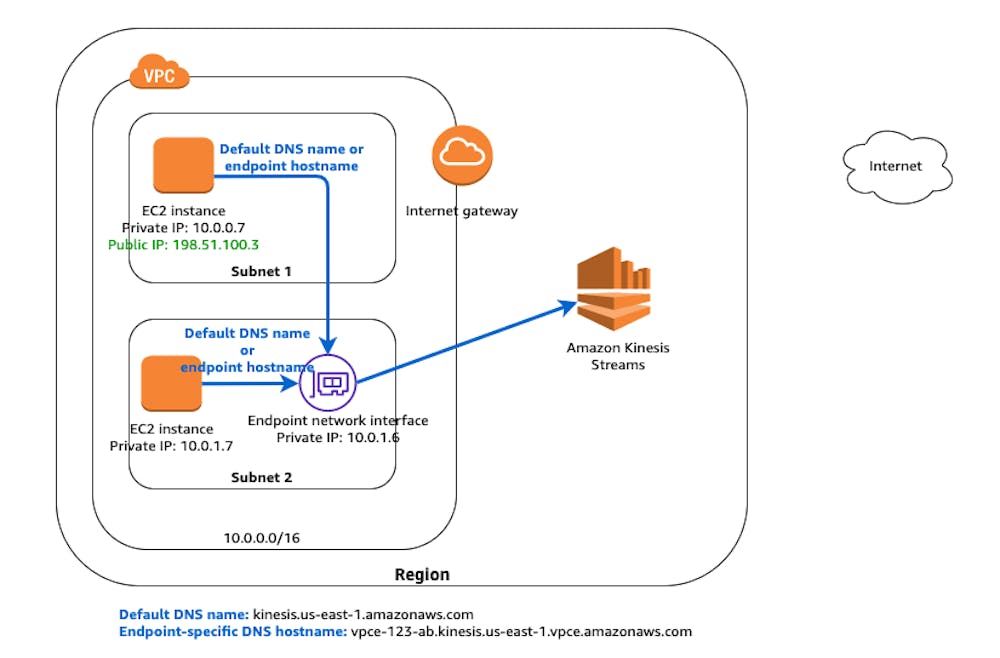
AWS Interface Endpoint
An interface VPC endpoint (interface endpoint) allows you to connect to services powered by AWS PrivateLink. These services include some AWS services, services hosted by other AWS customers and Partners in their own VPCs (referred to as endpoint services), and supported AWS Marketplace Partner services. The owner of the service is the service provider, and you, as the principal creating the interface endpoint, are the service consumer. (AWS)
Interface EndPoints uses DNS, not routing.
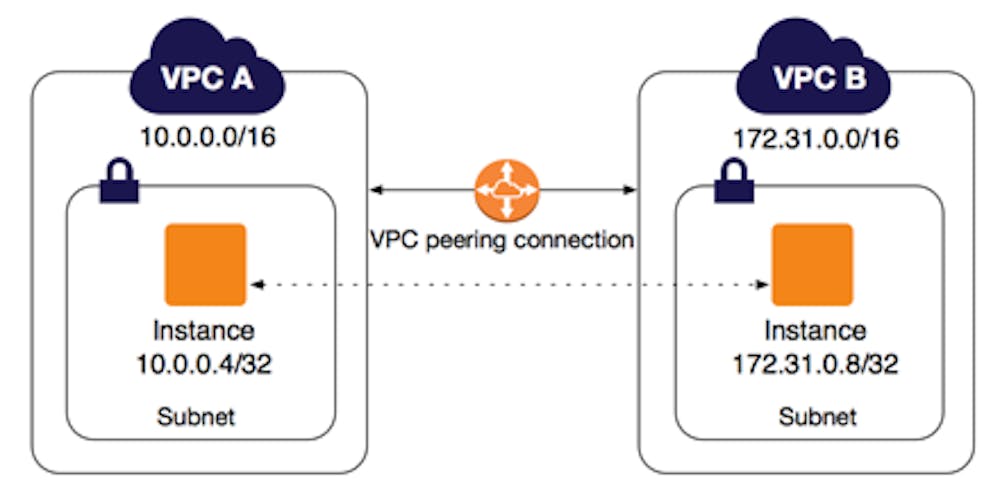
AWS VPC Peering
Allows you to connect VPC1 -> VPC2. It does not permit transitive connection:
If VPC2-> VPC3
Doesn't mean you have a connection to VPC1->VPC3, you will need to create a separate VPC Peering connection.
💙 Azure Discussion 💙
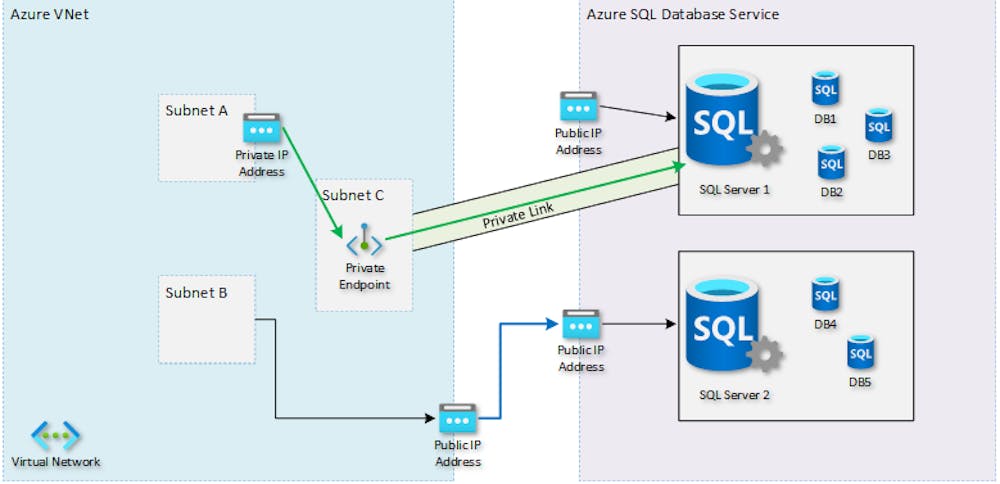
AWS Private EndPoint
Private endpoints allow ingress of traffic from your virtual network to an Azure resource securely. Private Link is a newer solution than Service Endpoints, introduced about a year ago. The key difference between Private Link and Service Endpoints is that with Private Link you are injecting the multi-tenant PaaS resource into your virtual network. With Service Endpoints, traffic still left you vNet and hit the public endpoint of the PaaS resource, with Private Link the PaaS resource sits within your vNet and gets a private IP on your vNet. When you send traffic to the PaaS resource, it does not leave the virtual network. (Samcogan.com)
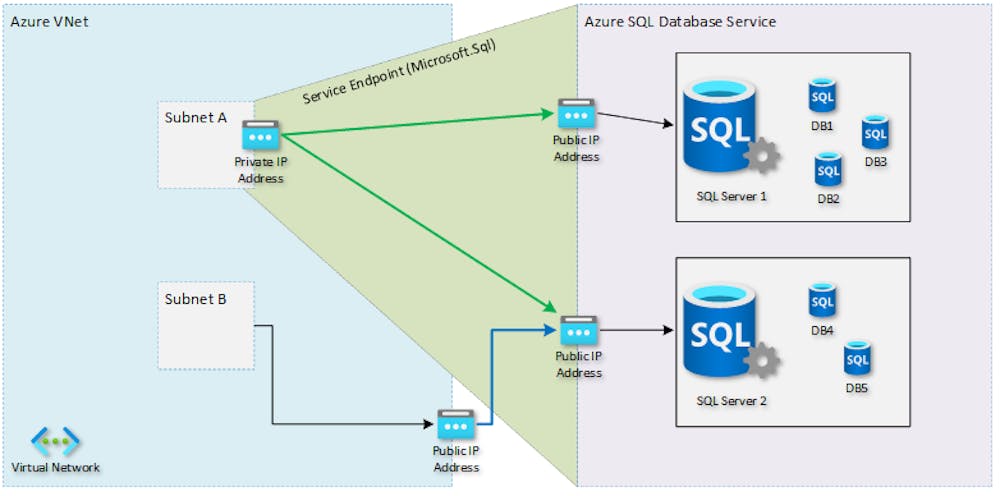
Azure Virtual Network Service EndPoint
Service endpoints provide secure and direct connectivity to Azure services over the Azure backbone network. Endpoints allow you to secure your Azure resources to only your virtual networks. Service endpoints enable private IP addresses in the VNet to reach an Azure service without the need of an outbound public IP. (Azure). Service Endpoints allow you to restrict access to your PaaS resources to traffic coming from your Azure Virtual Network. With Service Endpoints, the PaaS service is still separate to your vNet and traffic is leaving your virtual network to access the PaaS service. (SamCogan.com)
What should I use Private Endpoint or Service Endpoint?
As per Azure Documentation, they are encouraging to use Private EndPoint
Azure Virtual Network Peering
Virtual network peering enables you to seamlessly connect two or more Virtual Networks in Azure.