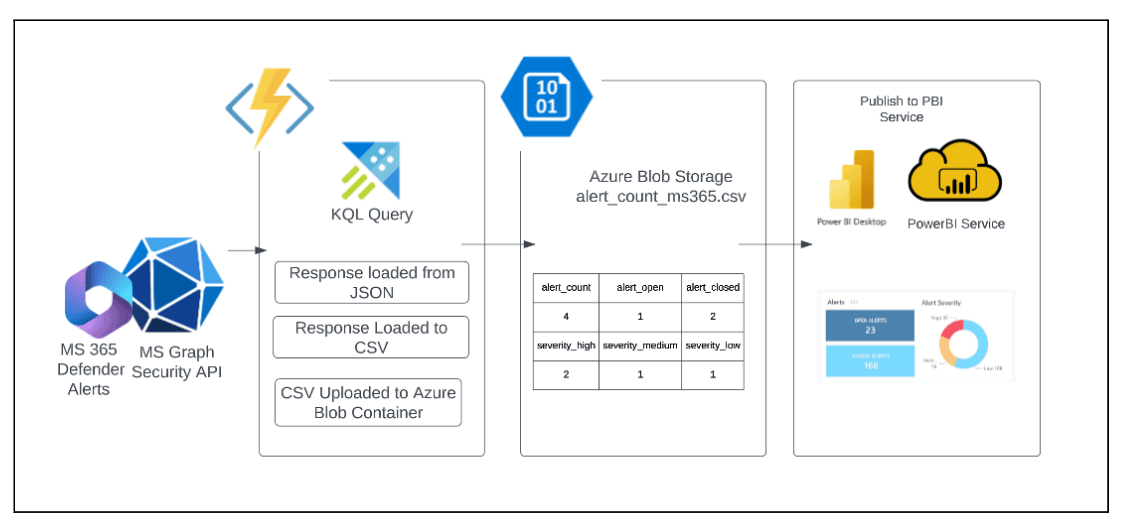
Using MS Graph API, 365 Defender, Azure Functions and PowerBI
High Level Plan
The architecture will begin with the use of the MS Graph Security API to fetch alerts from MS 365 Defender. This will be triggered using an Azure Function, which will then store the response in a CSV file. The CSV file will be loaded into Azure Blob Storage, where it can be accessed as a data source for Power BI. Power BI Desktop can be used to create and publish charts, which can be shared with others via the Power BI Service.
Cost Breakdown
* All costs are in Australia Central
* This excludes the licensing cost for Microsoft 365 E5 License and PowerBI Service Pro
* The cost breakdown is limited only to Alerts details.
Service | Description | Price (in USD/month) |
Azure Graph API | Security API | N/A |
Azure Functions | 1x, 128mb, 30 seconds execution time, (100 executions per day ), | 0.00 |
Azure Blob Storage | 1x, standard, GP2, Hot, LRS, 1GB, 10k Operations & Data Transfer, | 0.13 |
0.13 USD per month |
Detailed Plan
Table Contents
Useful Documents
Requirements
GamePlan
Insight: Table Matrix for Data Sources and Services
Useful Documents:
Microsoft Graph API - Security
https://learn.microsoft.com/en-us/graph/security-concept-overviewMicrosoft 365 Defender
- Microsoft Office 365 Defender
- Microsoft Office 365 Defender Alerts (Important)
Data Schema for KQL:
https://learn.microsoft.com/en-us/microsoft-365/security/defender/advanced-hunting-schema-tables?view=o365-worldwideMicrosoft 365 Defender API
https://learn.microsoft.com/en-us/microsoft-365/security/defender/api-hello-world?view=o365-worldwideMicrosoft Graph Security API? (provides a unified interface to access 365 API)
https://learn.microsoft.com/en-us/graph/api/resources/security-api-overview?view=graph-rest-1.0
Office 365 Security Documentation: https://github.com/MicrosoftDocs/microsoft-365-docs/tree/public/microsoft-365/security/office-365-security
Data source for PowerBI:
https://learn.microsoft.com/en-us/power-bi/connect-data/service-get-data
- Automate Creation of Alerts via Powershell:
https://learn.microsoft.com/en-us/powershell/module/exchange/new-activityalert?view=exchange-ps
2. Requirements
There are two ways to get started:
Create Microsoft 365 Developer account to access admin features such as (e.g. alerts). https://developer.microsoft.com/en-us/microsoft-365/dev-program
You are an admin of a Microsoft 365 with an Appropriate license. https://learn.microsoft.com/en-us/microsoft-365/security/defender/prerequisites?view=o365-worldwide
3. Gameplan
Data Source
Creating Microsoft 365 Alerts Mock Data
Working with Microsoft Graph API Security to extract data from MS 365 Defender.
Creating the Azure Function Application.
Visualizing Data. Developing via PowerBI Desktop
3.1 Data Source
A. Creating Microsoft 365 Alerts Mock Data.
Navigate to “Microsoft 365 Admin Center”. Under “Admin centers” group click “Security”. You will be directed to “Microsoft 365 Defender”
Microsoft 365 Defender services:
Microsoft Defender for Endpoint
Microsoft Defender for Office 365
Microsoft Defender for Identity
Microsoft Defender for Cloud Apps
Microsoft Defender Vulnerability Management
Azure Active Directory Identity Protection
Microsoft Data Loss Prevention
App Governance
* Microsoft unified these above services into what we called as “Microsoft 365 Defender”
Filter Alerts for Microsoft 365 Defender
It Creates a unified experience for security threats: Implement a filter of service sources using Microsoft Defender for Office 365 only.
You can filter alerts according to these criteria:
Severity
Status
Service sources (e.g. MDO - Office 365)
Entities (the impacted assets)
Automated investigation state
Image: Showing how to filter based on Service Sources
Creating Activity Rules / Alert Policies
Important: In order to create activity rules, then Auditing must be enabled. You can enable it under “Auditing” section under Compliance of Purview. It will be available 24-48 hrs.
Creation of Mock Alerts
I created a mock alert via these rules:
creating link with malware link from Eicar virus test
https://www.wicar.org/test-malware.html send URL links via gmail
Advanced policies such as activities can be created via the Advanced Policies section of Security.
IP Address from unknown location can be implemented by having an account signed in on TOR.
Image: Showing Alerts in M365 Defender Unified Portal
Very Important Key Links:
Purview: https://compliance.microsoft.com/compliancealertsv2
Security: https://security.microsoft.com/alerts?tid=cc1b978b-e786-4a39-a359-3e1b353d318b
3.2 Working with Microsoft Graph API Security to extract data from MS 365 Defender.
What is MS Graph API?
A tool for a unified access to the Microsoft ecosystem such as Microsoft 365.
- Provides Restful API
Compose of:
Microsoft Graph API: https://graph.microsoft.com a single endpoint accessible via REST API or SDKs
Microsoft Graph Connectors: Allows integration with other tools such as Jira to Microsoft 365. Bringing external data to Microsoft Graph.
Microsoft Graph Data Connect: Allows storing of large data in Azure Data Stores.
Supported Services: https://learn.microsoft.com/en-us/graph/overview-major-services?view=graph-rest-1.0
Microsoft Graph Explorer
A tool for you to learn GraphAPI: https://developer.microsoft.com/en-us/graph/graph-explorer
Sample Request on How to Query via Security API:
Microsoft Security API Authorization
https://learn.microsoft.com/en-us/graph/security-authorization
Using KQL for Advanced Hunting Query
3.3 Creating the Azure Function
The azure function application will perform these steps:
Authentication via Azure AD
Communicates with Azure Graph API Security
Fetch a query with the use of KQL
Load the response into a csv file (consume a lot of time and memory of Azure Function depending on size of json).
Upload the csv file into Azure Blob Container
Steps:
- Create an app registration in AAD to have access to Microsoft Graph API.
- Create an Azure Function App. Create a function with a Timer Trigger. Every 5 minutes.
Refer: Python Azure Function App: https://learn.microsoft.com/en-us/azure/azure-functions/functions-reference-python?tabs=asgi%2Capplication-level&pivots=python-mode-configuration
Refer: Github Link: https://github.com/asher-lab/azure-developer-demo/tree/main/azure-sample-m365-azfunction-pbi
- Connect your PowerBI Desktop to Azure Blob Storage. Create a PowerBI report.
4. Table Matrix for Data Sources and Services
https://www.scnsoft.com/services/business-intelligence/microsoft